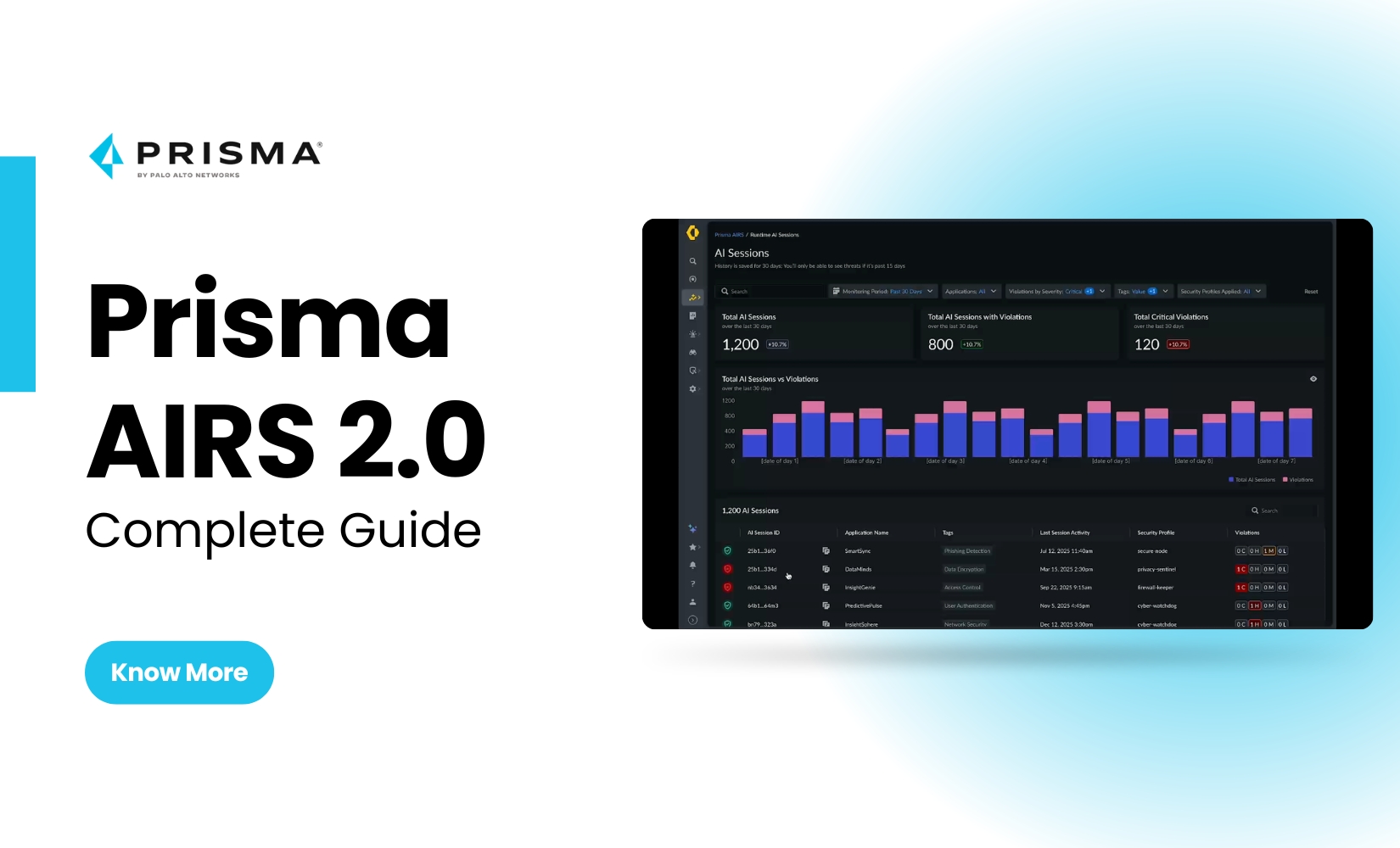
Securing AI systems has now become a critical business imperative in a world driven by AI innovation across industries. As AI models gain widespread acceptance, the risk of data poisoning, model theft, and adversarial manipulation also increases. Palo Alto Networks Prisma AIRS 2.0 is one such pioneering solution to handle these challenges with intelligent, proactive,...
Chennai, India
+91 72002 38417
+44 7399571124UK
+1 8668427277 USA
+61 479114075AUS